Introduction:
In the digital era, where technology governs every aspect of our lives, the threat landscape of cyberspace has grown exponentially. Cybersecurity has become a paramount concern as malicious actors continue to exploit vulnerabilities, putting individuals, businesses, and governments at risk. This article delves into the ever-changing world of cybersecurity, exploring its challenges, innovative solutions, and the way forward to safeguard our interconnected world.
The Pervasive Threats of Cybersecurity:
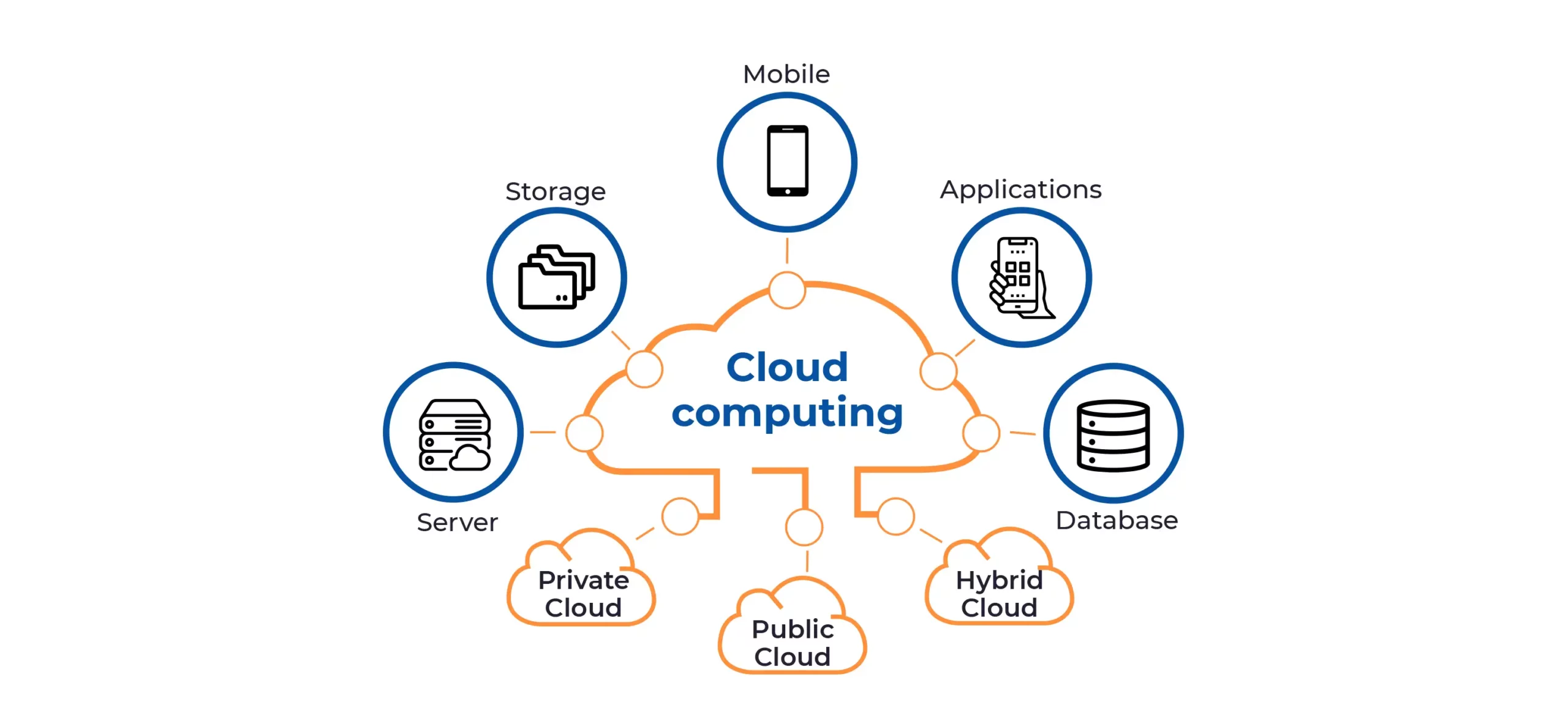
Cyber threats are diverse and constantly evolving, ranging from traditional malware and ransomware attacks to sophisticated nation-state-sponsored cyber warfare. With the proliferation of Internet of Things (IoT) devices, cloud computing, and interconnected networks, the attack surface has expanded drastically. These threats disrupt critical infrastructure, compromise personal data, and lead to financial losses on an unprecedented scale.
The Human Factor in Cybersecurity:
Despite advancements in technology, the human element remains a significant vulnerability in cybersecurity. Social engineering techniques such as phishing and spear-phishing continue to be highly effective in breaching secure networks. Cybercriminals exploit human emotions and tendencies to trick individuals into divulging sensitive information or clicking on malicious links. Comprehensive cybersecurity strategies must include education and awareness programs to empower users to recognize and resist such attacks.
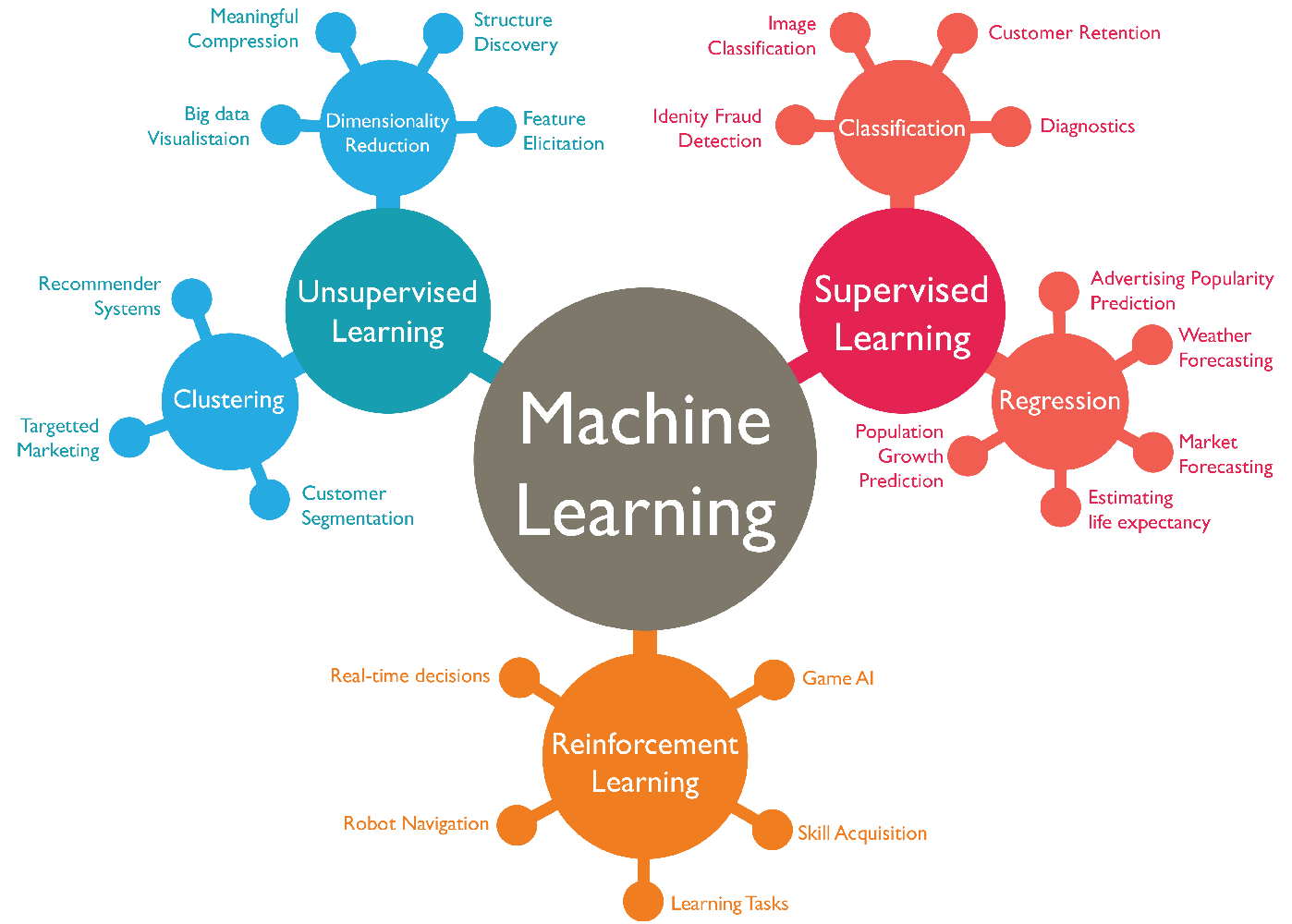
Artificial Intelligence and Machine Learning in Cybersecurity:
As the battle between attackers and defenders escalates, artificial intelligence (AI) and machine learning (ML) have emerged as powerful tools in cybersecurity. AI-driven systems can detect anomalies, predict potential threats, and respond to attacks faster than human counterparts. They enhance threat detection and response capabilities, allowing security teams to stay ahead of cyber adversaries.
Quantum Computing and the Future of Encryption:
With the advent of quantum computing, traditional encryption methods face unprecedented challenges. Quantum computers have the potential to break currently used encryption algorithms, exposing sensitive information. Post-quantum cryptography is an area of intense research to develop encryption methods that can withstand quantum attacks. Preparing for the quantum threat is a critical aspect of future-proofing cybersecurity.
Securing the Internet of Things (IoT):
The IoT revolution has brought convenience and efficiency to our lives, but it has also introduced new cybersecurity challenges. IoT devices often lack robust security measures, making them vulnerable to exploitation by cybercriminals. Compromised IoT devices can be used to launch large-scale DDoS attacks or invade privacy. Manufacturers must prioritize security by design and regular updates to mitigate these risks.
The Role of Governments in Cybersecurity:
Cybersecurity is not solely a responsibility for private entities; governments play a crucial role in protecting their citizens and critical infrastructure from cyber threats. Effective cybersecurity policies and regulations are needed to create a framework for cyber defense, information sharing, and incident response. International cooperation is also essential to tackle cross-border cybercrime and cyber-espionage.
Cyberwarfare and Nation-State Threats:
The lines between cybercrime and cyberwarfare have blurred, with nation-states employing cyber tactics as part of their military strategies. Advanced persistent threats (APTs) from nation-states pose significant challenges to national security and international stability. Defending against such attacks requires robust cyber defense capabilities and diplomatic efforts to establish norms of responsible state behavior in cyberspace.
Protecting Critical Infrastructure:
Critical infrastructure, such as power grids, transportation systems, and healthcare facilities, is increasingly reliant on interconnected technology. A successful cyber attack on these systems could have catastrophic consequences. Adopting a proactive and layered security approach is imperative to safeguard these vital assets from cyber threats.
The Rise of Bug Bounty Programs:
Bug bounty programs have gained popularity as an effective way to harness the collective intelligence of ethical hackers to identify and fix vulnerabilities. Companies and organizations offer rewards to researchers who responsibly disclose security flaws. These programs foster a strong security culture and encourage responsible disclosure, helping organizations strengthen their defenses.
Conclusion:
In conclusion, the world of cybersecurity is a constant battleground, where defenders must adapt and innovate to stay one step ahead of malicious actors. With the rapid evolution of technology, the threat landscape will continue to morph, necessitating agile and comprehensive cybersecurity measures. Embracing emerging technologies like AI and ML, preparing for quantum computing, and fostering collaboration between governments, industries, and individuals will be crucial in ensuring a secure digital future. Only through proactive efforts and a collective commitment can we build a resilient cyberspace that safeguards our societies and sustains technological progress.